Mobile Application Pentesting in 2026: Technical Challenges in an Increasingly Closed Ecosystem
Introduction
Mobile application pentesting has changed radically in recent years. In 2026, we are no longer talking only about finding obvious vulnerabilities in native applications, but about analyzing complex ecosystems where cross-platform frameworks, third-party SDKs, built-in anti-analysis protections, and increasingly restrictive operating systems converge.
The result is a landscape where many classic mobile pentesting techniques are still valid, but no longer sufficient on their own. Today, the value of mobile pentesting lies as much in technical depth as in the ability to adapt to new architectures, tools, and development models.
Cross-Platform Frameworks: Development Speed, New Risks
Frameworks such as Flutter, React Native, or .NET MAUI have become the default option for many organizations. From a development perspective, they offer clear advantages; from a pentesting perspective, they introduce new technical challenges.
Impact on Static Analysis
In native applications, static analysis typically focuses on:
- Java/Kotlin bytecode (Android)
- Swift/Objective-C binaries (iOS)
In cross-platform frameworks:
- Business logic resides in intermediate layers (for example, Dart compiled to native code in Flutter).
- Resulting binaries are often more obfuscated and less documented.
- Correlating source code with runtime behavior is more complex.
This forces the pentester to master framework-specific tooling and invest more time in reverse engineering to understand business flows, local validations, and API usage.
Impact on Dynamic and Network Analysis
A common technical scenario in 2026:
- The application ignores the system-level proxy configuration.
- Traffic cannot be intercepted without advanced instrumentation.
- The framework’s internal networking libraries bypass classic hooks.
In these scenarios, techniques such as dynamic hooking and in-memory instrumentation shift from optional to essential.
The Invisible Enemy: Defenses That Learn From the Attacker
Another key difference compared to previous years is that many applications now include active protections from the very beginning of the project.
Most Common Controls in 2026
- Root/jailbreak detection through multiple redundant checks.
- Emulator detection based on hardware, sensors, and behavioral signals.
- Runtime binary integrity verification.
- Protection against debugging and dynamic instrumentation.
- SSL pinning implemented at the framework or SDK level.
Realistic Technical Case
During a mobile audit:
- The application automatically closes when it detects Frida.
- Key features are disabled if a modified environment is detected.
- The session is invalidated if integrity checks fail.
In this context, pentesting stops being a simple execution of tools and becomes an iterative process of evasion, analysis, and validation of defensive controls.
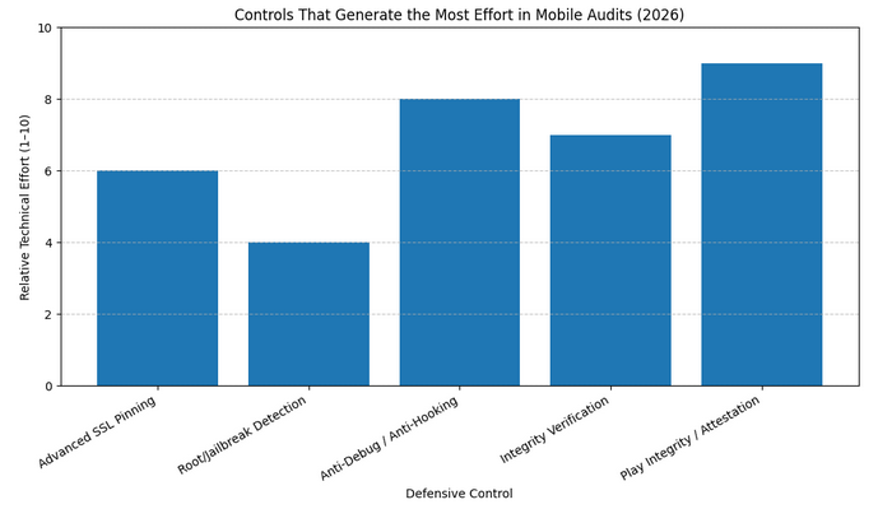 Estimated relative technical effort required to bypass different protection mechanisms in modern mobile applications. Values based on practical experience in advanced audits and hardened integrity environments.
Estimated relative technical effort required to bypass different protection mechanisms in modern mobile applications. Values based on practical experience in advanced audits and hardened integrity environments.
Increasingly Restrictive Mobile Operating Systems
Android and iOS have evolved toward more closed and controlled security models.
Key Changes in 2026
- Limited access to internal APIs.
- Stronger restrictions on debugging.
- Root and jailbreak are less stable and less representative of real users.
- Greater reliance on hardware-backed security and secure enclaves.
Direct Implications for Pentesting
Many classic techniques:
- Do not work on updated devices.
- Require version-specific exploits.
- Create unrealistic scenarios from a real-world risk perspective.
This has led to a shift in focus: less dependence on full system access and more emphasis on business logic, authentication flows, session management, and backend communication.
SSL Pinning, Modern Encryption, and Traffic Opacity
In 2026, intercepting mobile traffic is significantly more complex than in the past.
Technical Evolution
Today we commonly encounter:
- Widespread use of modern TLS.
- SSL pinning implemented at the SDK level.
- Additional certificate and environment validations.
- Protocols and configurations that complicate classic MITM attacks.
- Play Integrity / Device Attestation.
Typical Technical Scenario
In a controlled environment, the classic interception architecture is usually structured as follows:
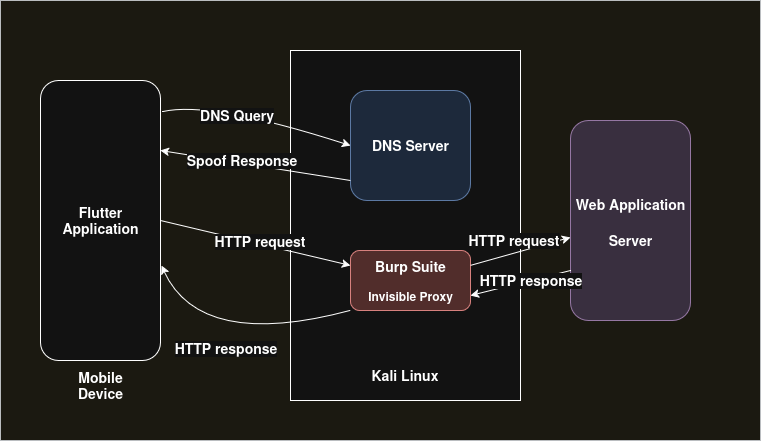 Traditional mobile traffic interception architecture using DNS spoofing and an invisible proxy (Burp Suite). This approach dominated for years but presents significant limitations against advanced pinning, TLS 1.3, and modern attestation mechanisms.
Traditional mobile traffic interception architecture using DNS spoofing and an invisible proxy (Burp Suite). This approach dominated for years but presents significant limitations against advanced pinning, TLS 1.3, and modern attestation mechanisms.
This setup represents:
- Controlled DNS resolution
- Response spoofing
- Invisible proxy (Burp)
- Forwarding to the real server
For years, this approach was sufficient. However, in 2026 it fails in multiple scenarios because:
- Pinning invalidates MITM.
- The environment is validated before the TLS handshake.
- Instrumentation is detected.
- Binary integrity is verified.
This reinforces a key idea: modern mobile pentesting requires coordination with development teams to achieve complete and actionable results.
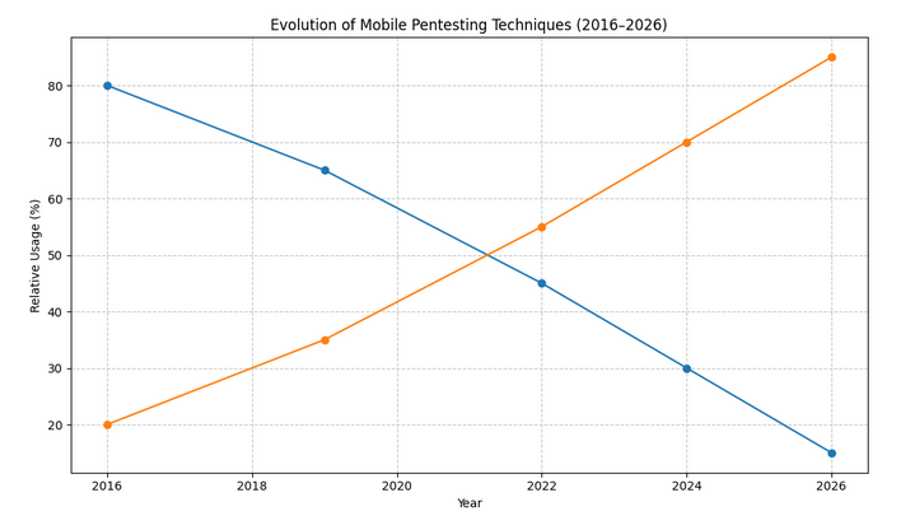 Estimated evolution of the relative weight of classic techniques (MITM, superficial reversing) versus modern techniques based on dynamic instrumentation and business logic analysis. Conceptual representation based on trends observed in mobile audits between 2016 and 2026.
Estimated evolution of the relative weight of classic techniques (MITM, superficial reversing) versus modern techniques based on dynamic instrumentation and business logic analysis. Conceptual representation based on trends observed in mobile audits between 2016 and 2026.
Third-Party Dependencies and SDKs: A Growing Attack Surface
Modern mobile applications integrate multiple external SDKs:
- Analytics
- Authentication
- Payments
- Advertising
- Monitoring
Each SDK:
- Adds additional permissions.
- Introduces its own logic and attack surface.
- May contain vulnerabilities or insecure practices.
Required Technical Approach
Pentesting must include:
- Enumeration of integrated SDKs.
- Analysis of permissions and data flows.
- Validation of configurations and versions.
- Evaluation of real privacy and security impact.
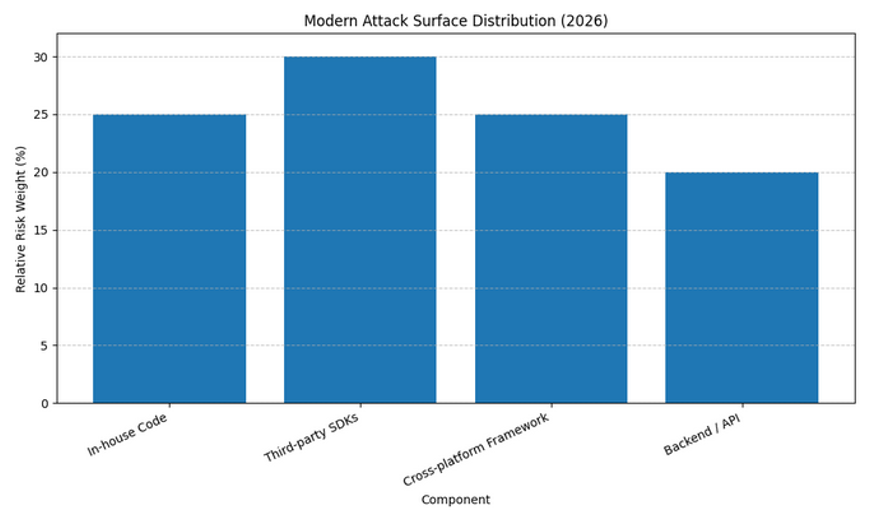 Conceptual distribution of the attack surface in modern mobile applications. Extensive integration of third-party SDKs and cross-platform frameworks significantly expands the effective analysis perimeter.
Conceptual distribution of the attack surface in modern mobile applications. Extensive integration of third-party SDKs and cross-platform frameworks significantly expands the effective analysis perimeter.
The Rise of AI-Powered Tools for Mobile Application Audits
In response to this growing complexity, a new generation of tools integrating artificial intelligence to assist in mobile application audits has emerged in 2026.
AI-Based Platforms
Tools such as Privado AI App Auditor use AI models to:
- Analyze mobile binaries.
- Identify sensitive data flows.
- Detect third-party SDKs and excessive permissions.
- Assess privacy and regulatory compliance risks.
These solutions are particularly strong in:
- Large-scale analysis.
- Continuous auditing.
- Early detection of structural risks.
Meanwhile, emerging platforms such as Perfai.ai explore agent-driven approaches, where AI not only detects issues but also proposes fixes, prioritizes risks, and integrates into development pipelines.
Current Limitations
Although these tools provide significant value:
- They do not replace deep manual analysis.
- They do not detect complex business logic flaws.
- They require expert validation to avoid false positives.
In practice, their greatest value lies in complementing traditional pentesting, not replacing it.
New Expectations and New Approaches in Mobile Pentesting
In 2026, modern mobile pentesting combines:
- Advanced static analysis.
- Selective runtime instrumentation.
- Architecture and design evaluation.
- Dependency and SDK auditing.
- Strategic use of AI-based tools.
- Close collaboration with development and DevOps teams.
The focus is no longer solely on “breaking” the application, but on understanding its real risk model and providing actionable recommendations aligned with business objectives.
Conclusion
Mobile application pentesting in 2026 is more demanding than ever. Cross-platform frameworks, built-in anti-analysis protections, restrictive operating systems, and new AI-based tools have completely redefined the landscape.
Organizations that understand this shift and adopt modern, hybrid, and collaborative approaches will be better prepared to protect applications that today represent one of the main assets — and attack vectors — of any digital business.
